FDA Recommends Cybersecurity Boost for Medical Devices
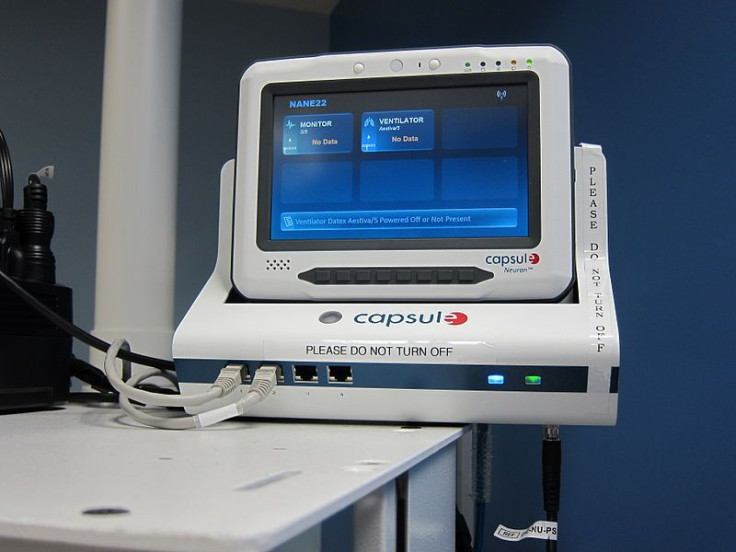
The Food and Drug Administration (FDA) issued an advisory in coordination with an alert from the Department of Homeland Security to medical device makers on Thursday, notifying them that cybersecurity on devices and hospital networks could be compromised, and that devices that aren't protected from malware or cyberattacks won't be approved for use.
The advisory comes after Philips fetal monitors, Oracle software, which is used in body fluid analysis machines, and other devices were shown to have vulnerabilities, PC World reported.
"The FDA is recommending that medical device manufacturers and health care facilities take steps to assure that appropriate safeguards are in place to reduce the risk of failure due to cyberattack, which could be initiated by the introduction of malware into the medical equipment or unauthorized access to configuration settings in medical devices and hospital networks," the FDA said.
The advisory cites the government's Industrial Control Systems Cyber Emergency Response Team website. The team enlisted Billy Rios and Terry McCorkle of cybersecurity firm Cylance, who told Reuters that they found over 300 pieces of compromised medical equipment.
"Over the past year, we've become increasingly aware of cybersecurity vulnerabilities in incidents that have been reported to us," William Maisel, deputy director for science at the FDA's Center for Devices and Radiological Health, told Reuters. "Hundreds of medical devices have been affected, involving dozens of manufacturers."
In October, there was a report of malware slowing down fetal monitors used on women with high-risk pregnancies at a Boston Hospital, while another case found that Oracle software was allowing remote access to databases in Roche Cobra analysis devices, an FDA spokeswoman told PC World.
The concern that Maisel raises is that a number of these devices are able to be controlled by default passwords easily found by hackers. With these passwords, they can remotely control the devices via the internet.
"Somebody could take over the device and make it do whatever they want it to do and it would be almost impossible for hospital staff to know that it had been tampered with," Rios said.
In the advisory, the FDA offered suggestions for both device manufacturers and health care facilities.
"Specifically, we recommend that manufacturers review their cybersecurity practices and policies to assure that appropriate safeguards are in place to prevent unauthorized access or modification to their medical devices or compromise the security of the hospital network that may be connected to the device," the FDA said.
They urged device makers to figure out ways to "limit unauthorized device access to trusted users only," especially for devices that are "life-sustaining" or connected to the hospital's network. In addition to this, they asked manufacturers to design ways to "maintain a devices critical functionality" when security has been compromised.
They asked health care facilities to restrict unauthorized access to networks, ensure antivirus software and firewalls are up to date, and monitor network activity, while developing strategies for maintaining critical functionality during adverse conditions.
"Cybersecurity incidents are increasingly likely and manufacturers should consider incident response plans that address the possibility of degraded operation and efficient restoration and recovery," the advisory said.
Published by Medicaldaily.com